E-commerce security protocols are standardized technical rules that govern the encryption, authentication, and integrity verification of data exchanged between online stores, payment gateways, and end users. These protocols operate at 4 distinct layers of the network stack: transport, application, authentication, and compliance.
Each layer addresses a specific attack vector, from packet interception to credential theft and fraudulent chargebacks.
The global cost of e-commerce fraud reached $48 billion in 2023, according to Juniper Research. This figure demonstrates that absent security protocols, every transaction endpoint becomes an exploitable vulnerability.
Security protocols are not optional configurations — they are the foundational infrastructure of trusted digital commerce.
Transport Layer Security (TLS) in E-commerce
TLS Protocol Versions and Deprecation
Transport Layer Security (TLS) encrypts data transmitted between a web browser and a web server. TLS 1.3, released in RFC 8446 in 2018, replaces TLS 1.2 as the minimum acceptable standard for e-commerce deployments.
TLS 1.0 and TLS 1.1 are deprecated by the Payment Card Industry Security Standards Council (PCI SSC) and are prohibited in compliant environments.
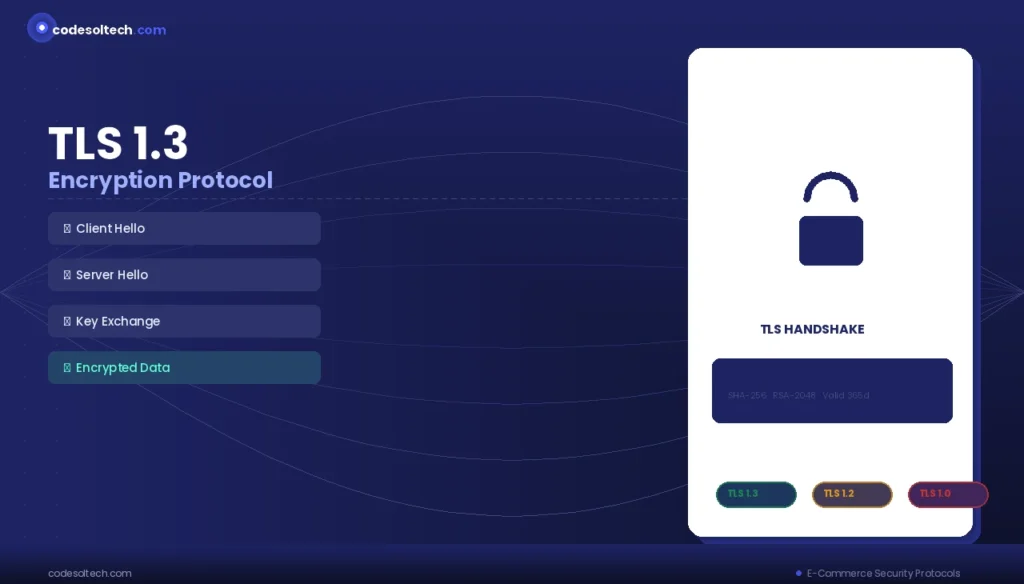
TLS 1.3 reduces the handshake from 2 round trips (TLS 1.2) to 1 round trip, lowering Time to First Byte (TTFB) by up to 100ms on high-latency connections. This performance gain directly improves Core Web Vitals scores, which Google incorporates into its page experience ranking signals.
TLS Certificate Types
E-commerce platforms deploy 3 types of TLS certificates based on validation level:
- Domain Validated (DV): Confirms domain ownership only; used for blogs and informational subdomains.
- Organization Validated (OV): Verifies organizational identity; used for corporate e-commerce portals.
- Extended Validation (EV): Requires legal entity verification; used by banks and enterprise checkout pages to trigger green-bar browser indicators.
Certificate expiration triggers browser security warnings that increase cart abandonment rates by up to 18%, according to Baymard Institute data. Automated certificate renewal via ACME protocol (used by Let’s Encrypt) eliminates manual expiration risk.
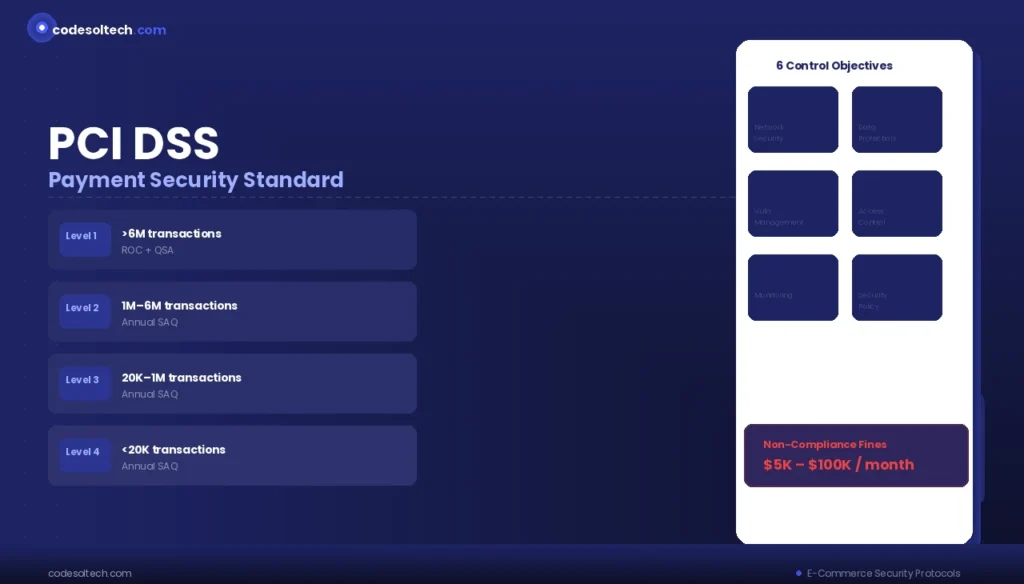
PCI DSS Compliance Framework
PCI DSS v4.0 Requirements
The Payment Card Industry Data Security Standard (PCI DSS) v4.0, published in March 2022, defines 12 core requirements across 6 control objectives for all entities that store, process, or transmit cardholder data. Compliance is mandatory for all merchants accepting Visa, Mastercard, American Express, Discover, or JCB card payments.
The 6 control objectives of PCI DSS v4.0 are:
- Network Security: Deploy and maintain firewalls and network segmentation to isolate the Cardholder Data Environment (CDE).
- Data Protection: Encrypt stored Primary Account Numbers (PAN) using AES-256 or RSA-2048 at minimum.
- Vulnerability Management: Install anti-malware software and maintain patched systems on a 30-day cycle.
- Access Control: Implement Role-Based Access Control (RBAC) and restrict CDE access to authorized personnel only.
- Monitoring and Testing: Log all access to network resources and cardholder data; retain logs for a minimum of 12 months.
- Information Security Policy: Maintain a documented security policy reviewed at least once every 12 months.
PCI DSS Merchant Levels
PCI DSS classifies merchants into 4 levels based on annual transaction volume:
- Level 1: More than 6 million Visa or Mastercard transactions per year; requires an annual Report on Compliance (ROC) by a Qualified Security Assessor (QSA).
- Level 2: 1 million to 6 million transactions per year; requires an annual Self-Assessment Questionnaire (SAQ).
- Level 3: 20,000 to 1 million e-commerce transactions per year; requires an annual SAQ.
- Level 4: Fewer than 20,000 e-commerce transactions per year; requires an annual SAQ.
Non-compliance with PCI DSS results in fines ranging from $5,000 to $100,000 per month, imposed by acquiring banks on behalf of card brands.
Authentication Protocols for E-commerce
OAuth 2.0 and OpenID Connect
OAuth 2.0 is an authorization framework defined in RFC 6749 that enables third-party applications to access user resources without exposing credentials. E-commerce platforms integrate OAuth 2.0 to support social login (Google, Facebook, Apple) and to authorize payment services, fulfillment APIs, and marketing platforms.
OpenID Connect (OIDC) extends OAuth 2.0 with an identity layer, delivering a JSON Web Token (JWT) that contains verified user identity claims. OIDC reduces account registration friction and cuts checkout abandonment by removing forced account creation steps.
Multi-Factor Authentication (MFA)
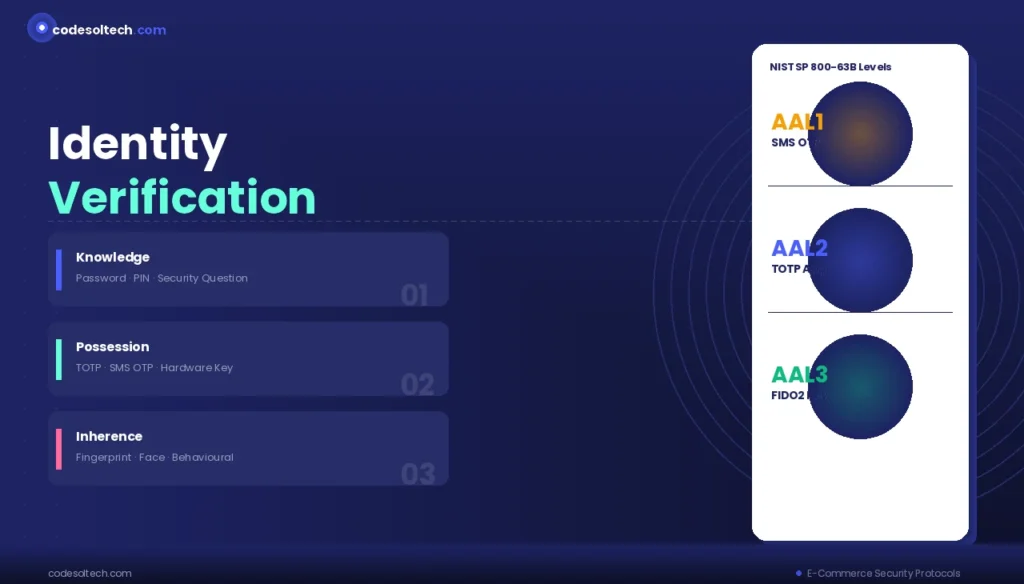
Multi-Factor Authentication (MFA) enforces identity verification through 2 or more independent factors:
- Knowledge factor: Password or security question.
- Possession factor: TOTP (Time-based One-Time Password) via authenticator app or SMS OTP.
- Inherence factor: Biometric data (fingerprint, face recognition).
NIST Special Publication 800-63B classifies SMS OTP as Authentication Assurance Level 1 (AAL1) due to SIM-swapping vulnerabilities. TOTP applications (Google Authenticator, Authy) achieve AAL2. FIDO2/WebAuthn hardware security keys achieve AAL3, the highest assurance level defined by NIST.
3-D Secure 2 (3DS2) Protocol
3DS2 Architecture
3-D Secure 2 (3DS2), defined by EMVCo in specification version 2.3.1, is a payment authentication protocol that performs real-time risk assessment on card-not-present (CNP) transactions. 3DS2 replaces the legacy 3DS1 protocol, which relied on browser redirects and static passwords.
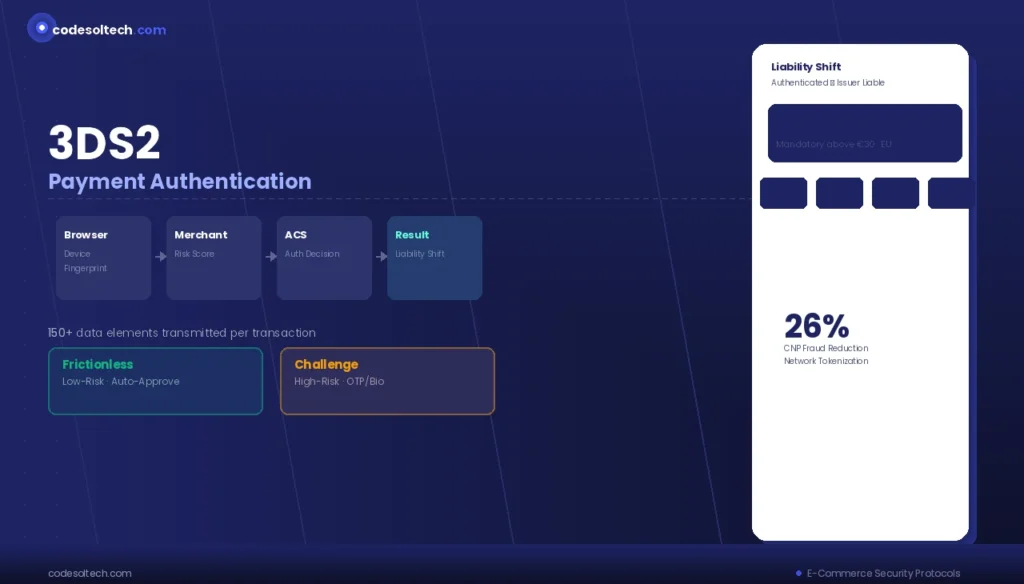
3DS2 transmits over 150 data elements — including device fingerprint, transaction history, and behavioral biometrics — to the card issuer’s Access Control Server (ACS). The ACS executes a frictionless authentication flow for low-risk transactions and triggers a challenge flow (biometric or OTP) for high-risk ones.
3DS2 Liability Shift
3DS2 authentication transfers fraud liability from the merchant to the card issuer. Merchants who implement 3DS2 correctly are exempt from chargeback liability on successfully authenticated transactions. Liability shift applies specifically to transactions authenticated via the 3DS2 protocol, not those processed through the frictionless flow without issuer approval.
The European Union’s PSD2 (Payment Services Directive 2) mandates Strong Customer Authentication (SCA) for all online transactions exceeding €30, requiring 3DS2 compliance for all EU-facing e-commerce checkouts.
Content Security Policy (CSP) and JavaScript Security
CSP Headers for E-commerce
Content Security Policy (CSP) is an HTTP response header that instructs browsers to load resources only from pre-approved origins. E-commerce platforms deploy CSP headers to prevent Cross-Site Scripting (XSS) and Magecart-style skimming attacks that inject malicious JavaScript into checkout forms.
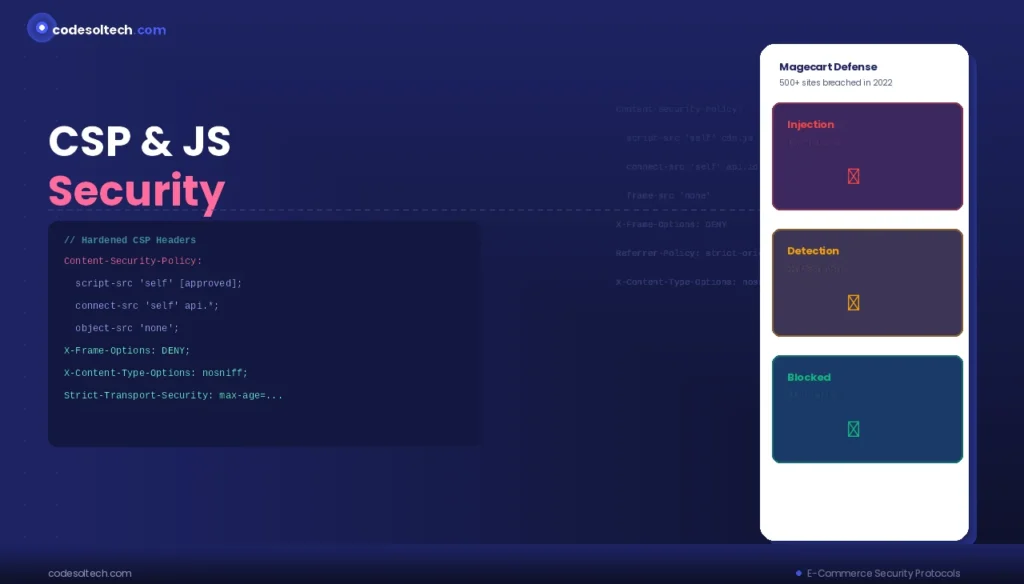
A hardened CSP for an e-commerce checkout page restricts:
script-src: Allowed JavaScript origins (e.g., payment SDKs, analytics).connect-src: Permitted API endpoints for form data submission.frame-src: Allowed iframe origins for 3DS2 challenge windows.object-src 'none': Blocks all plugin-based execution vectors.
Magecart attacks compromised over 500 e-commerce websites in 2022 alone, according to Sansec research, by injecting JavaScript skimmers into checkout pages. CSP headers with report-uri directives enable real-time violation reporting to detect injection attempts.
Subresource Integrity (SRI)
Subresource Integrity (SRI) is a browser security feature that validates external script integrity using a cryptographic hash. E-commerce developers append a integrity attribute containing a SHA-256, SHA-384, or SHA-512 hash to every <script> and <link> tag loading external resources. Browsers reject any resource whose content does not match the declared hash, neutralizing supply-chain injection attacks on CDN-hosted libraries.
Fraud Detection and Risk Scoring Protocols
Device Fingerprinting
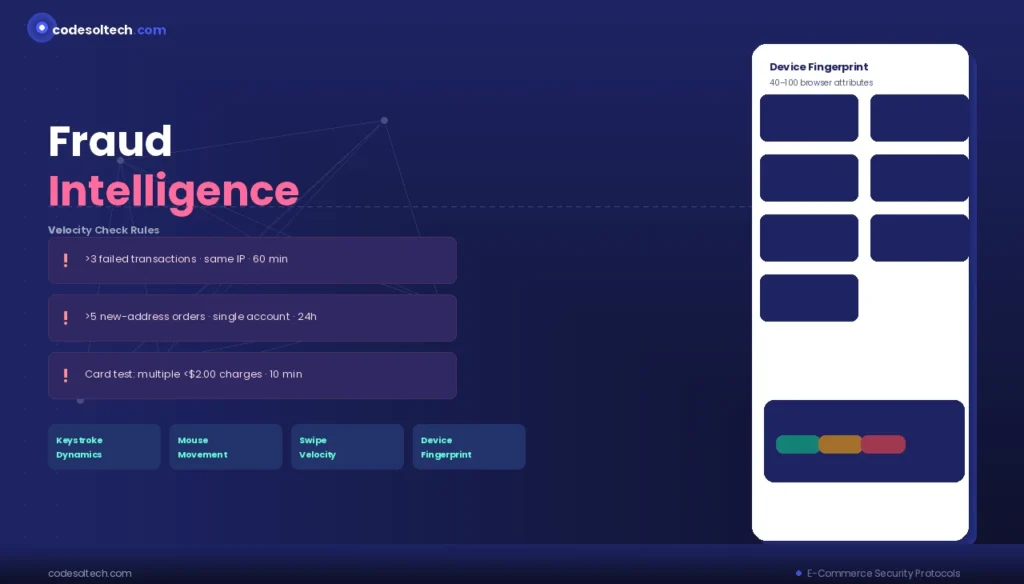
Device fingerprinting collects 40 to 100 browser and hardware attributes including User-Agent string, screen resolution, installed fonts, WebGL renderer, and canvas fingerprint to generate a persistent device identifier without cookies.
Payment processors use device fingerprints to correlate transactions across sessions and flag account takeover (ATO) attempts.
Velocity Checks and Behavioral Biometrics
Velocity check protocols flag transactions that exceed predefined thresholds within a fixed time window. 3 common velocity rules applied by fraud engines are:
- More than 3 declined transactions from a single IP address within 60 minutes.
- More than 5 orders shipping to a new address within 24 hours on a single account.
- Card testing patterns: multiple low-value charges (under $2.00) within 10 minutes.
Behavioral biometrics — keystroke dynamics, mouse movement patterns, and swipe velocity — provide continuous authentication signals that distinguish legitimate users from automated bots executing credential stuffing or carding attacks.
HTTPS and HSTS Deployment
HTTP Strict Transport Security (HSTS)
HTTP Strict Transport Security (HSTS) is an HTTP response header defined in RFC 6797 that instructs browsers to connect exclusively over HTTPS for a specified duration.
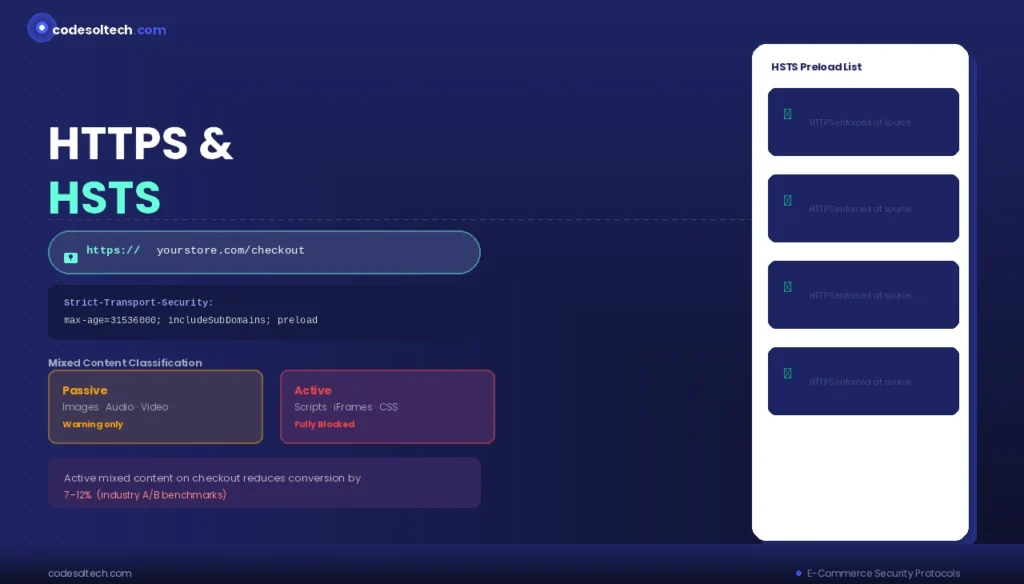
E-commerce sites configure HSTS with a max-age value of at least 31,536,000 seconds (1 year) to satisfy Google’s HTTPS ranking requirements and PCI DSS Requirement 4.2.1.
HSTS preloading submits a domain to the browser-maintained HSTS preload list, hardcoding HTTPS-only behavior into Chrome, Firefox, Safari, and Edge at the browser source level. Preloading eliminates the window of vulnerability during the first visit before the HSTS header is received.
Mixed Content Blocking
Mixed content errors occur when an HTTPS page loads HTTP resources (images, scripts, iframes). Browsers classify mixed content into 2 categories:
- Passive mixed content: Non-interactive resources (images, audio, video) — browsers display a warning but load the resource.
- Active mixed content: Scripts, iframes, and stylesheets — browsers block these resources entirely and flag the page as insecure.
Active mixed content on checkout pages triggers browser security warnings that reduce conversion rates by 7% to 12%, based on industry A/B testing benchmarks.
API Security Protocols for E-commerce Integrations
API Authentication Methods
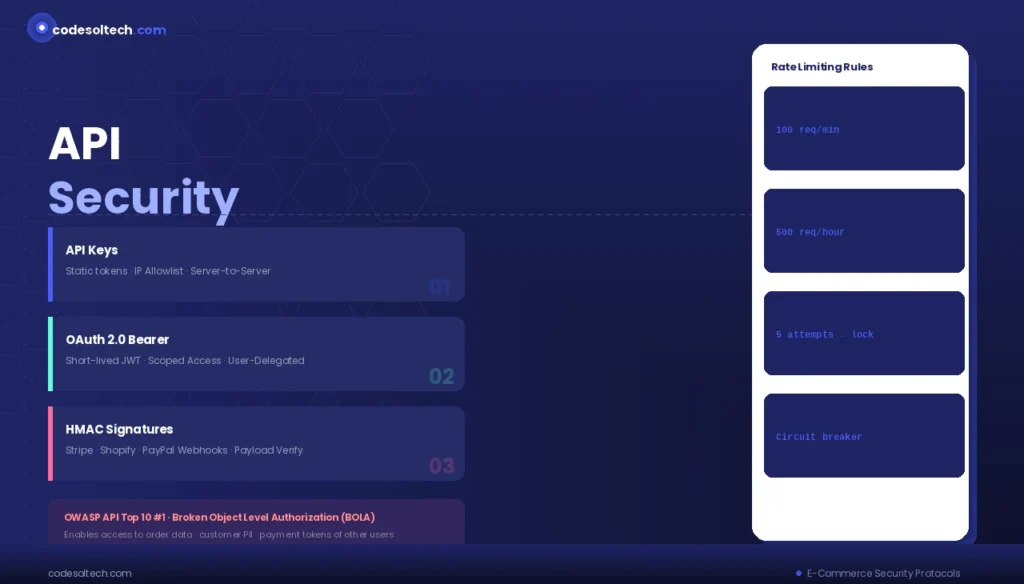
E-commerce platforms expose APIs to payment gateways, inventory systems, shipping carriers, and ERP integrations. 3 standard API authentication methods used in e-commerce are:
- API Keys: Static tokens transmitted in HTTP headers; suitable for server-to-server communication with IP allowlisting.
- OAuth 2.0 Bearer Tokens: Short-lived JWT access tokens with defined scopes; used for user-delegated API access.
- HMAC Signatures: Keyed-hash message authentication code signatures on request payloads; used by Stripe, Shopify, and PayPal webhooks to verify event origin.
Rate Limiting and OWASP API Security Top 10
Rate limiting enforces a maximum number of API requests per time unit per client to prevent brute force attacks and denial-of-service (DoS) conditions.
The OWASP API Security Top 10 (2023) identifies Broken Object Level Authorization (BOLA) as the most critical API vulnerability in e-commerce environments, enabling attackers to access order data, customer PII, and payment tokens belonging to other users by manipulating resource identifiers in API requests.
Data Encryption Standards for Stored Payment Data
Tokenization vs. Encryption
Tokenization replaces sensitive cardholder data (PAN, CVV, expiration date) with a non-sensitive token that has no exploitable mathematical relationship to the original data. Encryption transforms plaintext data into ciphertext using a cryptographic key, which remains recoverable if the key is compromised.
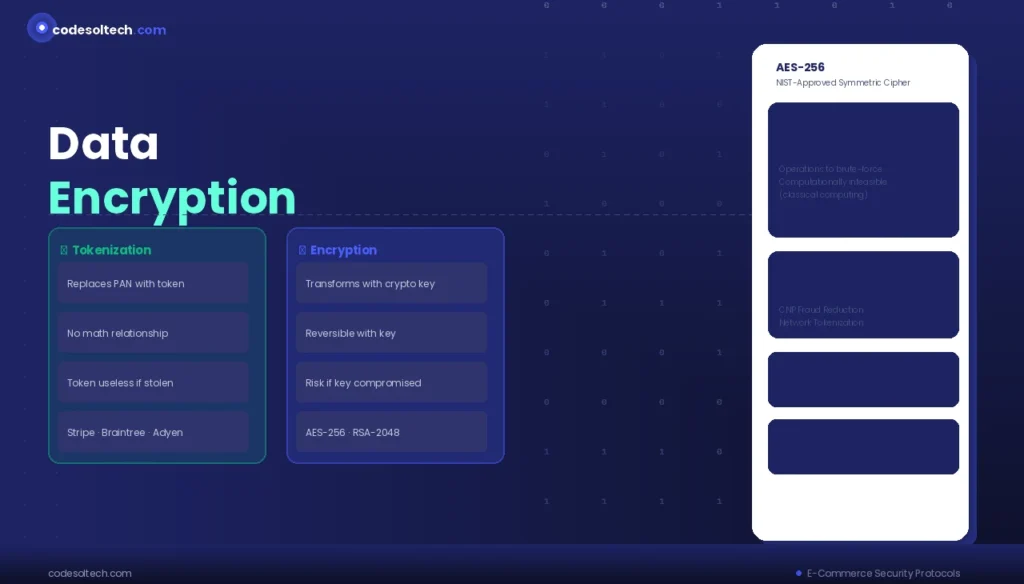
PCI DSS mandates tokenization or point-to-point encryption (P2PE) for all cardholder data at rest. Stripe, Braintree, and Adyen implement network tokenization using card network-issued tokens (Visa Token Service, Mastercard Digital Enablement Service) that bind the token to the merchant, reducing CNP fraud rates by up to 26%.
AES-256 Encryption
The Advanced Encryption Standard with 256-bit key length (AES-256) is the NIST-approved symmetric encryption algorithm for protecting sensitive e-commerce data. AES-256 encrypts customer PII, stored credentials, and internal API secrets. A brute-force attack against AES-256 requires 2^256 operations — computationally infeasible with current or projected classical computing resources.
Security Headers Checklist for E-commerce Platforms
A fully hardened e-commerce HTTP response includes the following 7 security headers:
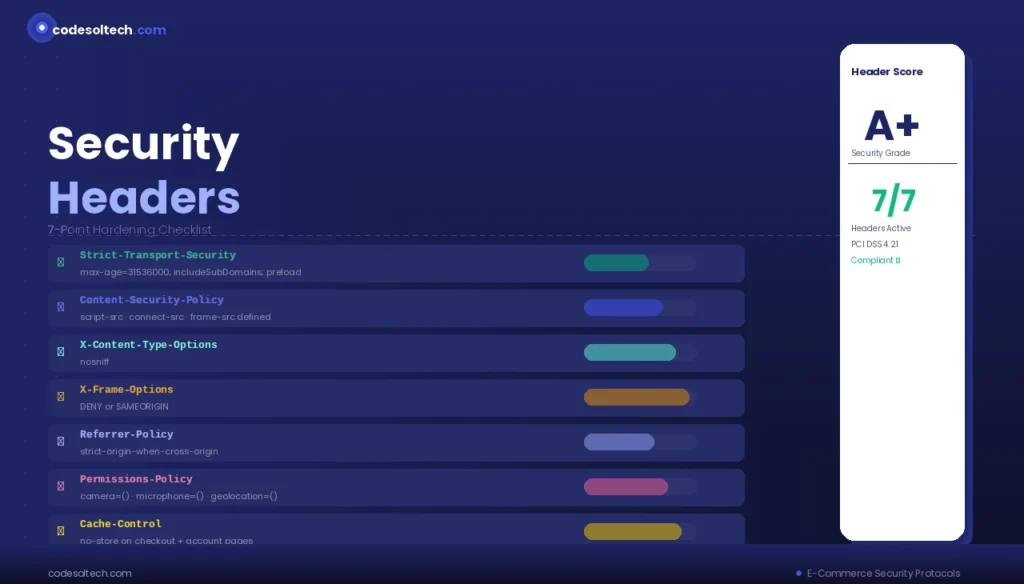
- Strict-Transport-Security:
max-age=31536000; includeSubDomains; preload - Content-Security-Policy: Defines approved script, style, and connection origins.
- X-Content-Type-Options:
nosniff— prevents MIME-type sniffing attacks. - X-Frame-Options:
DENYorSAMEORIGIN— prevents clickjacking on checkout frames. - Referrer-Policy:
strict-origin-when-cross-origin— limits referrer data leakage to third parties. - Permissions-Policy: Restricts browser feature access (camera, microphone, geolocation) to declared origins.
- Cache-Control:
no-storeon checkout and account pages — prevents sensitive data caching.
Final Words
E-commerce security protocols form a layered defense architecture spanning transport encryption, authentication, payment standards, and API hardening.
TLS 1.3, PCI DSS v4.0, 3DS2, OAuth 2.0, and CSP headers each address distinct threat vectors that collectively protect transaction integrity, customer data, and merchant revenue.
Implementing all protocol layers reduces fraud exposure, achieves compliance, and builds the consumer trust that converts browsers into buyers.